Dear Manufacturer and Vendors,
I’ve been thinking about management tools, dashboards, and ‘Single Panes of Glass’ (SPOG) a lot recently. I’ve been considering what makes them useful, how they can be improved, and what I need in them. I’ve come to a conclusion:

I hate the term ‘Single Pane of Glass’ (SPoG).Your dashboard doesn’t even come close to that promise. Instead, you have delivered SPIN: Single PAIN in (my) Network.
Before building your next dashboard and calling it a SPoG, I suggest asking yourself these questions:
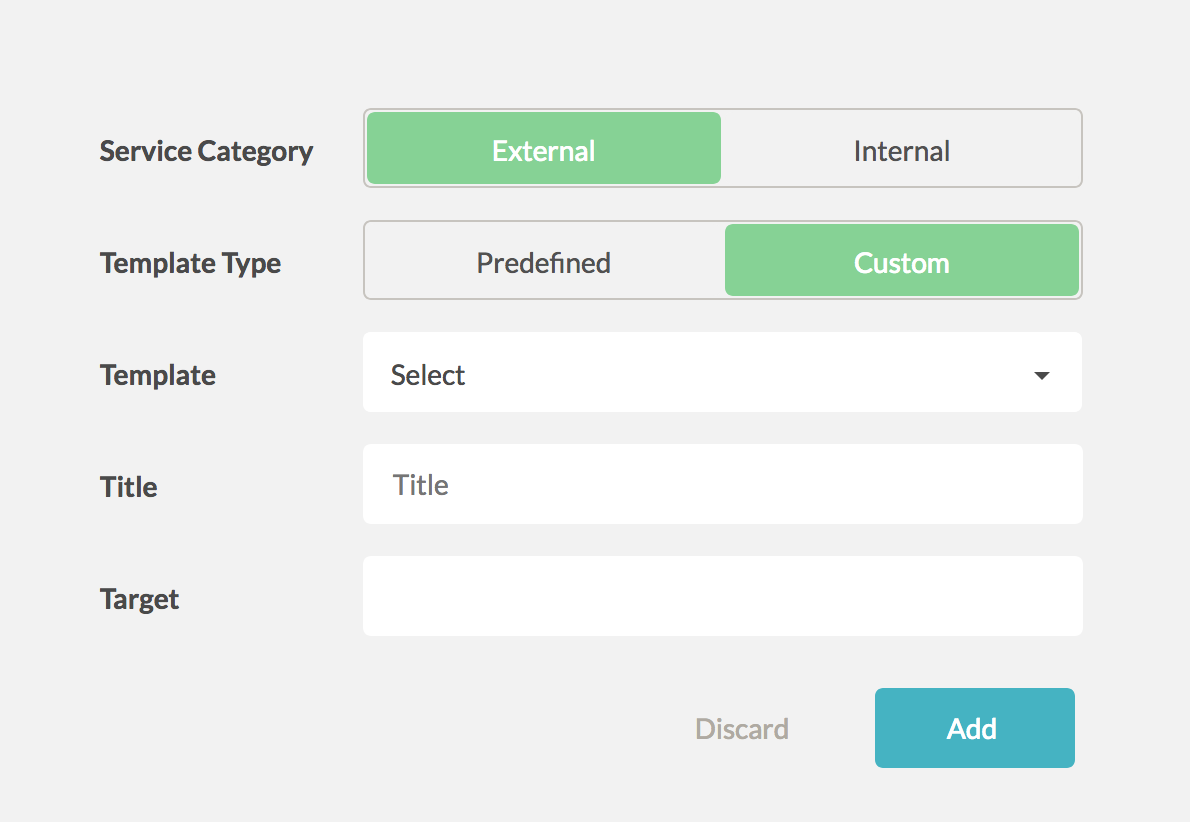
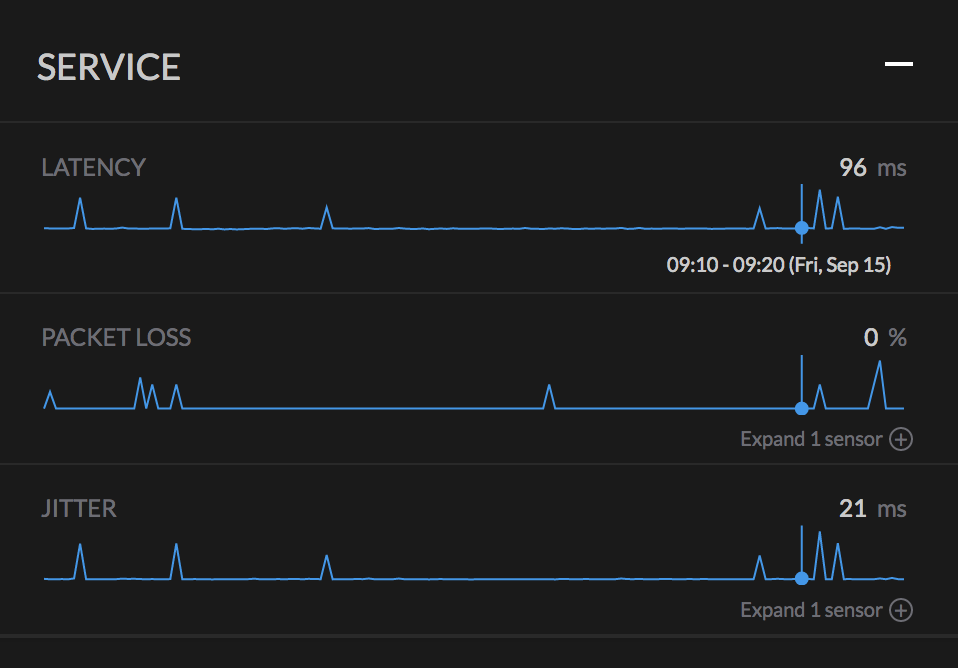
- Can my dashboard display information that exists outside of your product? None of us work on a single technology. We must work and understand more of the network or application stack. If you can’t provide basic reporting on those directly impacting layers that your product must rely on, it’s not a SPoG.
- Can the dashboard consume or interact with the API’s of your other dashboards? I get that you might avoid integrating closely with your competitors. However, if you can’t even integrate with the other system and dashboards provided by your own company, you have failed.
- Does the dashboard follow standard design rules and elements of all of your other dashboards and tools, or is this a one-off design that will require the average user to learn a whole new interface and the series of bugs that are sure to reveal themselves?
- Does your API follow a similar schema to your other applications and dashboards? You do have an API, right?
- Does your dashboard require custom licensing for each feature? If you spend more time developing licensing requirements than API’s, integration support with other products, or visibility of the other layers, it’s not a SPoG.
I get that many IT manufacturers have a vast inventory of products. I understand the question of “how much is too much information?” So, I would like to offer a few things to consider.
- Build a common API schema standard. Force all business units to adhere to it as closely as possible.
- Build a common aesthetic. Common menu types, common graph elements, standard filters, etc.
- To answer the question “how much is enough information,” I also have a suggestion. When building new certification exams, the first step is a Job Tasks Analysis (JTA). That process is about defining the common knowledge, tools, and methodologies used by someone in that role. A JTA should be the FIRST step in building new monitoring and management tools. That gathered data should drive every decision regarding tools, views, or information provided by your dashboard.


 So, in 2017 when
So, in 2017 when 

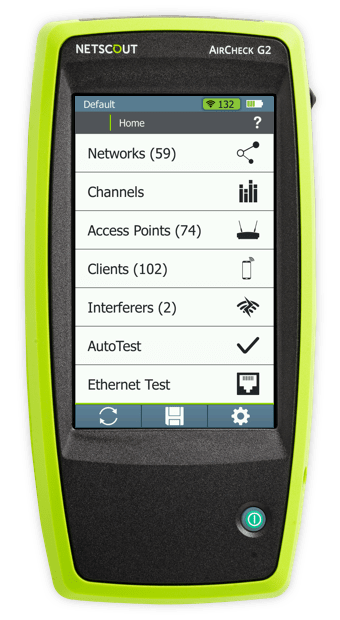
 devices which don’t follow the 802.11 standard, and long delays in problem resolution are all part of the experience.
devices which don’t follow the 802.11 standard, and long delays in problem resolution are all part of the experience.
 moving on to the next assignment, and that perfect design last through the weekend. Now the engineer is located in a different state, working on a different project, and is getting calls from the customer.
moving on to the next assignment, and that perfect design last through the weekend. Now the engineer is located in a different state, working on a different project, and is getting calls from the customer.